Cyber threats have become more sophisticated, automated, and financially motivated than ever before. From ransomware shutting down hospitals to phishing scams targeting remote workers, modern digital risks evolve daily. As attack surfaces expand across cloud platforms, mobile devices, and connected home networks, individuals and businesses alike need layered protection that goes beyond basic antivirus software.
TLDR: A small stack of carefully selected cybersecurity apps can defend against up to 95% of modern digital threats when combined strategically. This includes next-generation antivirus, password managers, VPNs, firewalls, endpoint detection tools, phishing protection, and cloud security platforms. Together, these tools create layered defense against malware, ransomware, identity theft, and data breaches. Investing in comprehensive protection dramatically reduces vulnerability in today’s threat landscape.
Below are seven cybersecurity apps and platforms that, when used together, form a powerful defense system against the vast majority of digital attacks seen today.
Contents
1. Next-Generation Antivirus (NGAV)
Traditional antivirus software relied heavily on signature-based detection. Modern threats, however, mutate too quickly for signature databases alone. Next-generation antivirus (NGAV) uses artificial intelligence, behavioral monitoring, and machine learning to detect suspicious patterns before malware fully executes.
Key protection features include:
- Behavior-based detection for zero-day attacks
- Ransomware rollback capabilities
- Exploit prevention for browser and system vulnerabilities
- Real-time threat intelligence updates
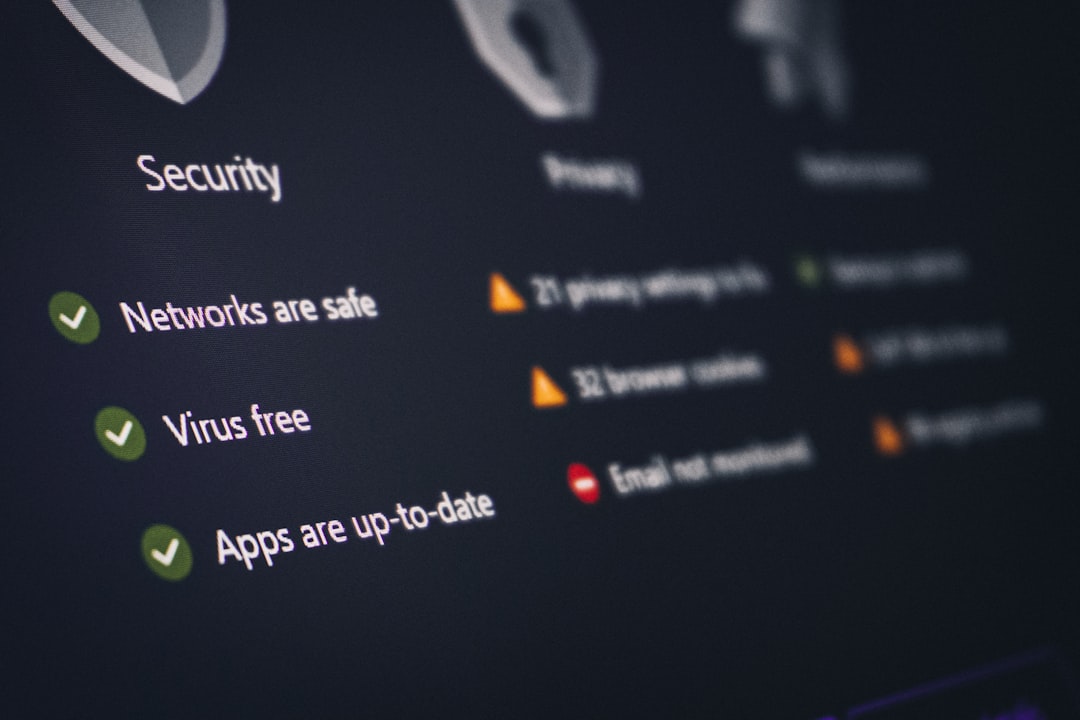
NGAV acts as the foundation of modern digital security. Without it, devices remain exposed to malware variants that traditional systems may not recognize.
2. Password Manager with Dark Web Monitoring
Weak and reused passwords are responsible for a significant percentage of breaches. A secure password manager generates complex, unique passwords and stores them in encrypted vaults.
Advanced features often include:
- 256-bit AES encryption
- Dark web monitoring alerts
- Secure password sharing
- Multi-factor authentication (MFA) integration
By eliminating predictable passwords and enabling password hygiene at scale, password managers drastically reduce the risk of credential-stuffing and brute-force attacks.
3. Virtual Private Network (VPN)
Public Wi-Fi networks remain one of the easiest entry points for attackers. A Virtual Private Network encrypts internet traffic, masking IP addresses and protecting data transmission from interception.
Benefits include:
- End-to-end encryption
- IP masking for privacy protection
- Protection against man-in-the-middle attacks
- Secure remote access
For remote workers and frequent travelers, VPNs are essential. They significantly reduce exposure to data sniffing and session hijacking attempts.
4. Advanced Firewall Protection
Firewalls serve as gatekeepers between trusted internal networks and untrusted external traffic. Modern firewall applications go beyond basic packet filtering and incorporate intelligent inspection systems.
Advanced firewall apps provide:
- Intrusion detection and prevention systems (IDS/IPS)
- Application-layer filtering
- Geo-blocking capabilities
- Real-time traffic monitoring dashboards
When properly configured, firewalls block a significant volume of malicious traffic before it reaches internal systems.
5. Endpoint Detection and Response (EDR)
While antivirus focuses on prevention, Endpoint Detection and Response (EDR) focuses on visibility and rapid remediation. EDR apps continuously monitor endpoints such as laptops, desktops, and mobile devices for suspicious activity.
Core capabilities include:
- Continuous behavior monitoring
- Automated threat containment
- Forensic analysis tools
- Incident response automation
Modern targeted attacks often bypass initial defenses. EDR ensures that if malware slips through, it can be quickly isolated and neutralized before spreading across a network.
6. Anti-Phishing and Email Security Tools
Email remains the number one attack vector in modern cybersecurity. Phishing attacks have evolved into convincing spear-phishing campaigns and business email compromise (BEC) scams.
Dedicated phishing defense apps provide:
- AI-driven email scanning
- Malicious link sandboxing
- Attachment behavior analysis
- Domain spoofing detection
By filtering suspicious messages before they reach inboxes, these tools significantly reduce human-error-related breaches.
7. Cloud Security and Backup Solutions
Cloud services power everything from document storage to enterprise infrastructure. Cloud security apps protect sensitive data through encryption, monitoring, and backup automation.
Essential features include:
- End-to-end cloud encryption
- Misconfiguration detection
- Automated compliance monitoring
- Ransomware-resistant backups

Automated backups remain one of the most effective defenses against ransomware. Even if systems are compromised, secure backups ensure business continuity.
Comparison Chart of the 7 Cybersecurity Apps
| App Category | Primary Function | Best Against | Ideal For |
|---|---|---|---|
| Next-Gen Antivirus | Real-time malware detection | Viruses, ransomware, zero-day threats | All users |
| Password Manager | Secure credential storage | Credential theft, brute force attacks | Individuals, teams |
| VPN | Encrypted internet browsing | Man-in-the-middle attacks | Remote workers |
| Advanced Firewall | Network traffic filtering | Network intrusion attempts | Home and business networks |
| EDR | Endpoint monitoring and response | Advanced persistent threats | Businesses |
| Email Security | Phishing prevention | Spear phishing, BEC | Email-heavy organizations |
| Cloud Security & Backup | Data protection and recovery | Ransomware, data loss | Cloud users and enterprises |
Why These 7 Tools Cover 95% of Modern Threats
Today’s cyberattacks generally fall into a few major categories:
- Malware and ransomware
- Credential theft
- Phishing and social engineering
- Network intrusions
- Data loss and cloud misconfigurations
Each of the seven cybersecurity apps targets one or more of these categories. When layered together, they create defense in depth, a strategy where multiple protective measures overlap to reduce single points of failure.
No single tool provides perfect protection. However, combining prevention, detection, response, and recovery mechanisms significantly reduces risk exposure. Organizations implementing layered cybersecurity strategies report dramatically fewer successful breaches.
FAQ
1. Do individuals really need all seven cybersecurity apps?
Most individuals benefit from at least four: next-gen antivirus, password manager, VPN, and secure cloud backup. The others become increasingly important for businesses and remote teams handling sensitive data.
2. Isn’t built-in operating system security enough?
Built-in protections provide a strong starting point but often lack advanced threat detection, dark web monitoring, or enterprise-grade incident response capabilities. Supplemental apps enhance overall protection.
3. Can free cybersecurity apps provide adequate protection?
Free tools can cover basic needs but typically lack advanced features such as ransomware rollback, real-time monitoring, or automated response mechanisms. Premium versions often provide stronger multi-layered protection.
4. What is the most common modern cyber threat?
Phishing remains the most common attack vector, frequently serving as the entry point for ransomware and credential compromise incidents.
5. How often should cybersecurity apps be updated?
Applications should update automatically whenever possible. Real-time threat intelligence feeds are essential, as new malware variants appear daily.
6. Are VPNs necessary if using HTTPS websites?
HTTPS encrypts website communication, but a VPN encrypts all device traffic and protects against broader network-based attacks, especially on public networks.
7. What is the biggest cybersecurity mistake organizations make?
Relying on a single security tool instead of implementing layered defense. A multi-app strategy dramatically reduces risk and limits the damage if one layer fails.
In a world where digital threats evolve constantly, cybersecurity is no longer optional. By implementing these seven essential cybersecurity apps, users and organizations can defend against the overwhelming majority of modern attacks. The right combination fosters resilience, reduces financial risk, and ensures that when threats strike, they are detected, contained, and neutralized swiftly.




